Facebook SDK Vulnerability Puts Millions of Users Accounts at Stake
The Security researchers from leader in intelligent led Mobile Risk Management (MRM), MetaIntell have found out a major vulnerability in the latest version of Facebook SDK that puts millions of Facebook user’s authentication tokens at stake.
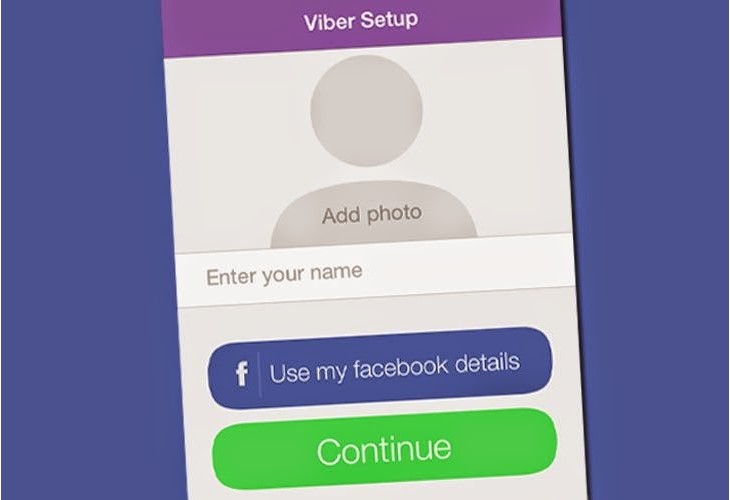
Facebook SDK is perhaps the easiest way for iOS and Android to integrate the mobile apps with Facebook that provides support for logging in using Facebook platform, reading and writing to Facebook APIs, and much more.
The OAuth authentication of Facebook or “Login as Facebook” is a secure way of signing into other third party apps without sharing the passwords. After the user has approved the permissions as requested by the application, the Facebook SDK implements the OAuth 2.0 User-Agent flow to retrieve the secret user’s access token required by the apps in order to call Facebook APIs to read, write or modify the data of the users of Facebook on their behalf.
It is quite important not to share your secret token with anyone, but Facebook SDK stores it in an unencrypted format that can be accessed easily.
Moreover, any third party app with the access to the device file system can easily read this file and can easily steal the token of Facebook remotely.
MetaIntell team has already told the Facebook team regarding the vulnerability, but Facebook is not looking in the mood to update its SDK by fixing the current issues. All the current iOS and Android apps are vulnerable to this kind of attack.
In order to be saved from the vulnerability of Facebook SDK, you don’t need to login into 3rd party apps using Facebook account. App developers are advised to remove the secret tokens of access of the users from device file system in order to secure online storage with encrypted channel.