Security researchers have sounded the alarm over a new ‘professionally developed’ malware that harvests users account for anything, from identity theft to credentials selling, propaganda campaigns, and malvertising.
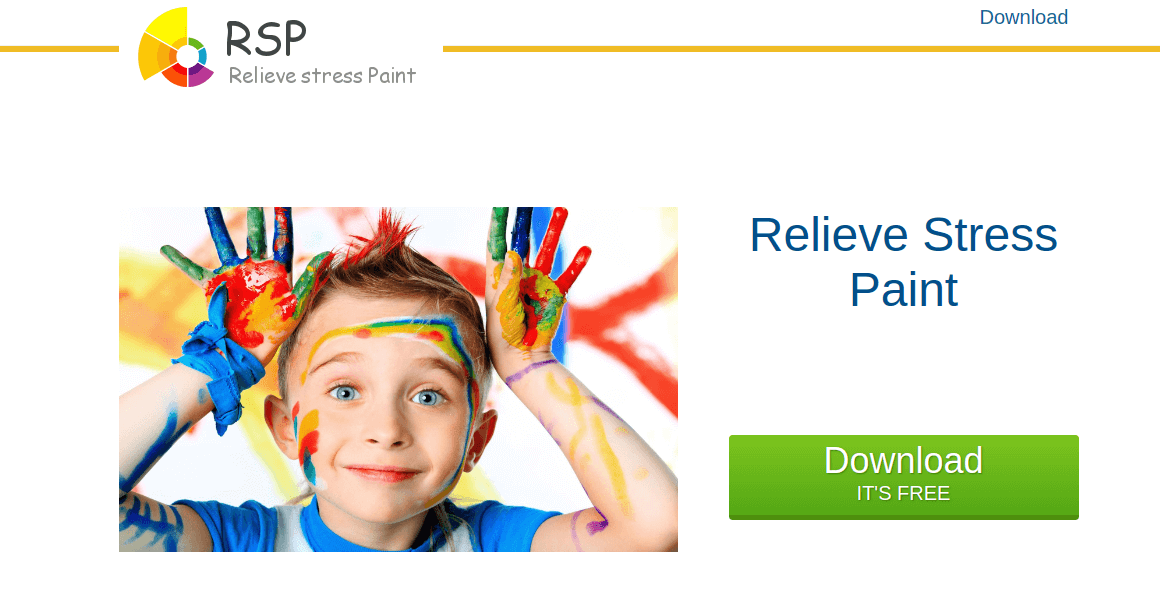
The malware gets to infect your device when you download a certain painting software that is passing off as a stress reliever; except it will soon start adding more stress to your life. The application is nothing more than a front for malware designed to steal your Facebook credentials and credit card details.
The malware first appeared on security experts’ radar early last week, and by Friday it has infected over 45,000 Facebook users. The StressPaint malware appears to be more interested in users who manage Facebook pages and had configured a payment method with their account.
The malware was first made public by Radware, who said it was quickly spreading around the world with such a high infection rate. Experts believe the speed of the infection “indicates this malware was developed professionally.”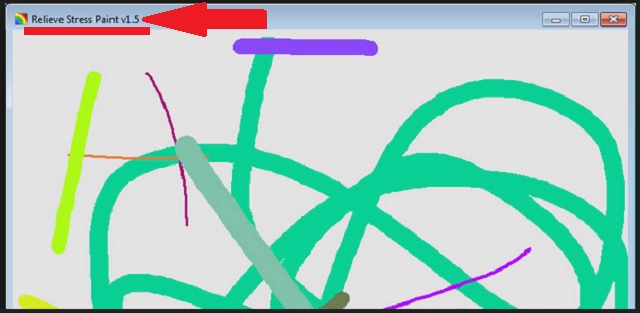
The security researchers further say that the malware could soon start targeting Amazon user in its future campaigns. They reached that conclusion after discovering malware’s control panel had a section dedicated to Amazon accounts breaching.
How the infection is happening
The infection campaign is happening via email phishing, where the user is socially engineered to visit a fake AOL site. Where they get to see the ‘Relieve Stress Paint’ download. If a user decides to download the software and run the file, a window will open up showing just the basic painting program to the user. Then give them the impression that nothing suspicious is happening, all the while the malware is running in the background.
When the user first launched the ‘Relieve Stress Paint’ application, immediately the malware runs in the background and start dropping files onto the system and start looking for information it can steal. It steals information by copying the content of Chrome browser’s cookies and login date files. If it finds saved Facebook credentials, it sends them to a C2 server.
Once the information is successfully stolen, more information is collected on the compromised account; information such as number of friends, pages managed, and the payment methods set up.
“Security tools, like antivirus or endpoint detection and response, always look for suspicious active processes on the system and general credential stealing methods like key logging or hooking,” said Adi Raff, the leader of a security research team at Radware.
“We believe that the process of the malware is only active on the system for less than a minute on specific occasions (like first run, computer restart, and stress pain tool rerun) and that the data theft is done from a copy of Chrome files (cookies/login data) which helps the malware stay undetected.”