The world has never been as crazy about cryptocurrency as it is now, and all signs show this is just the beginning. Miners have become so crypto-craze that all ethics have been thrown out of the windows.
Previously, when you went all online, all you had to worry about is a hacker trying to steal your identity, install some ransomware on your computer or spy on you. Well, on that list of things to worry about when you go online, you can now add cryptocurrency miners using your CPU without your permission.
As annoying as it is, it a reality that when you go online, there are hackers stealthily implanting weird JavaScript on your computer that use your CPU processing power to mine them cryptos.
You can tell someone else is using your computer for crypto-mining by the CPU overclocking more than it should with respect to the numbers and weight of the apps you are currently running. If you think the high CPU clocking you are experiencing is unwarranted based on the apps you are currently running, there is a possibility you are not the only person using your computer at that time.
The hackers wait until you are online browsing to start using your CPU thanks to the JavaScript they implanted on your computer. Though it does take some level of technical skills to know if your computer has been compromised.
Things just got worse
Previously, if you detected crypto-miners piggy-backing on your CPU, you could cut them off immediately by closing the browser. Well, it seems they have found a workaround that temporary solution, by improving the code of the JavaScript they implant on your computer. Right now, it does not matter whether or not the browser is open; the code will execute in the background and continue mining cryptos for them.
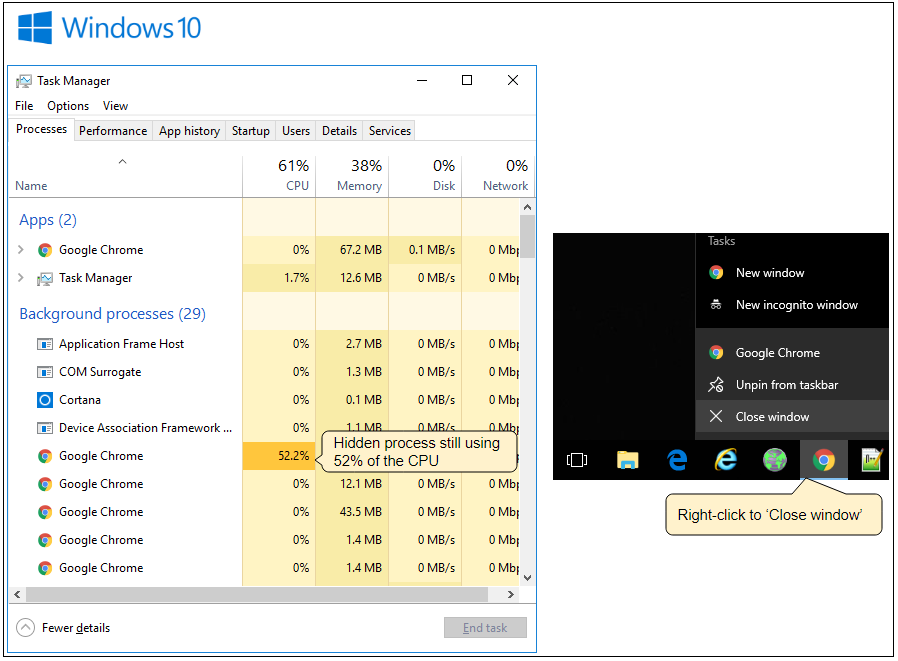
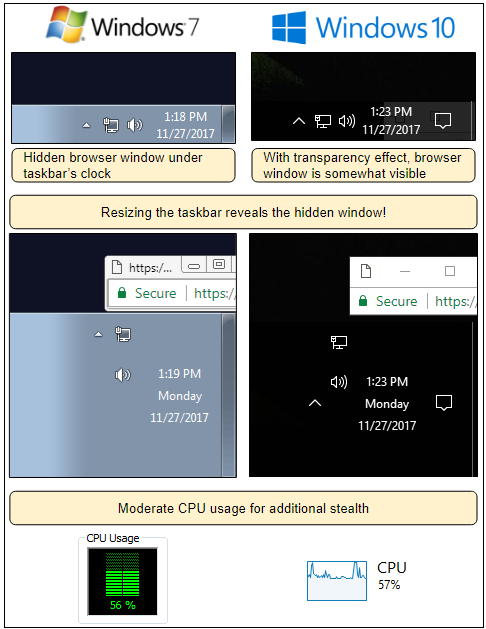
The security company Malwarebytes unearthed this new improved JavaScript able to mine even when the browser is closed. The company says these new JavaScript are built using the same technique used for online advertising model called ‘pop-under.’ They are used to load hidden ads, and they make sure the windows cannot be closed easily. They often sit behind the taskbar, meaning the average user won’t even realize they are there in the first place.
“The trick is that although the visible browser windows are closed, there is hidden one that remains opened. This is due to a pop-under which is sized to fit right under the taskbar and hides behind the clock,” explains Malwarebytes.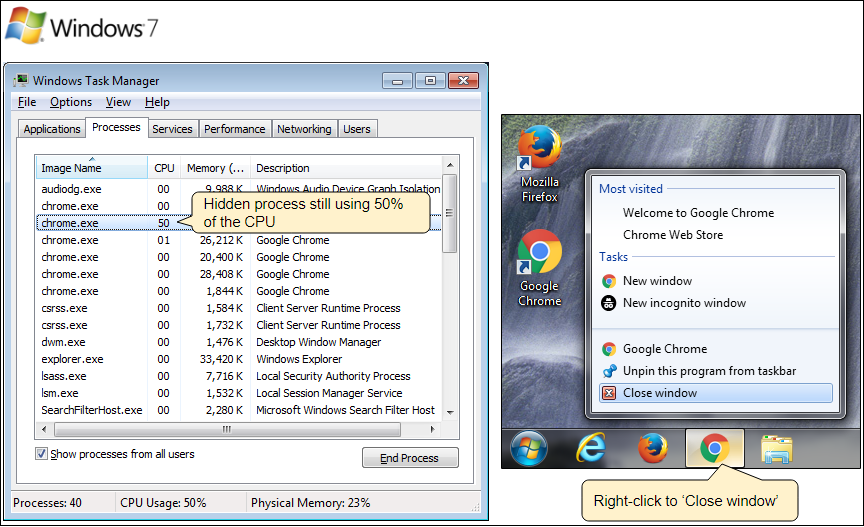
Crypto-Miners cause no damage in the strictest sense
You might find it hard to believe that crypto-miners in the strictest sense pose no danger to your online safety and security. Some of them would say they have no interest in snooping in your files and activities both online and offline on your computer. They are just interested in using part of your CPU to mine them some cryptos; well, without your permission of course!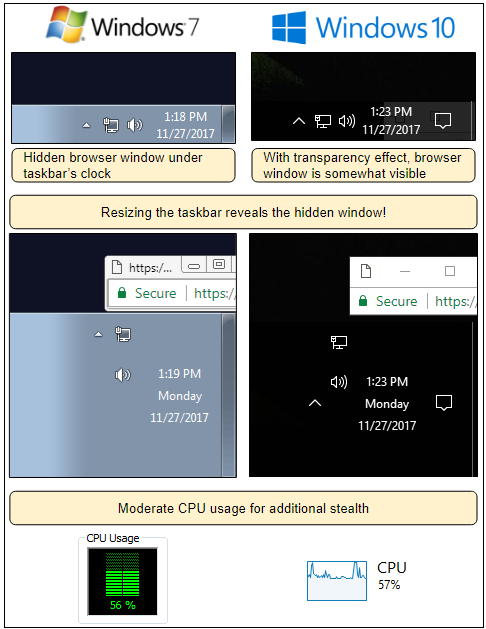
Nonetheless, it does not make it ethical or legal, and they are actually trespassing on your own piece of property, your CPU, computer resources, and broadband. For that reason they should be stopped and even arrested, for that reason, security firms have begun blocking Coinhive, which was initially designed as a legitimate initiative.
“Forced mining (no opt-in) is a bad practice, and any tricks like the one detailed in this blog are only going to erode any confidence some might have had in mining as an ad replacement,” writes Malwarebytes on its blog post.
“Unscrupulous website owners and miscreants alike will no doubt continue to seek ways to deliver drive-by mining, and users will try to fight back by downloading more adblockers, extensions, and other tools to protect themselves. If malvertising wasn’t bad enough as it, now it has a new weapon that works on all platforms and browsers.”